| Line 14: | Line 14: | ||
---- | ---- | ||
---- | ---- | ||
| − | == | + | ==Introduction to cryptography == |
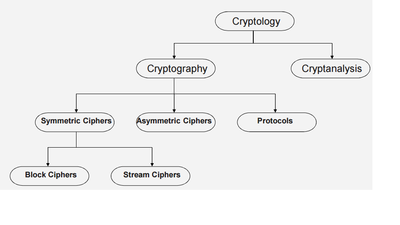
The block diagram below shows an overview of the field of cryptology. | The block diagram below shows an overview of the field of cryptology. | ||
| − | [[File:OverviewCrypt.png| | + | [[File:OverviewCrypt.png|400px|thumb|left|Fig 1: Overview of field of Cryptology]] |
'''Cryptography''' is the science of secret writing with the goal to hide the orginal message. | '''Cryptography''' is the science of secret writing with the goal to hide the orginal message. | ||
| Line 25: | Line 25: | ||
Cryptography itself splits into three main branches: | Cryptography itself splits into three main branches: | ||
| − | 1. | + | ==== 1. Symmetric Algorithms : ==== |
* Also known as private-key, single-key or secret-key cryptography | * Also known as private-key, single-key or secret-key cryptography | ||
| − | [[File:SymCrypt.png| | + | [[File:SymCrypt.png|400px|thumb|left|Fig 2: Symmetric Cryptography Basics]] |
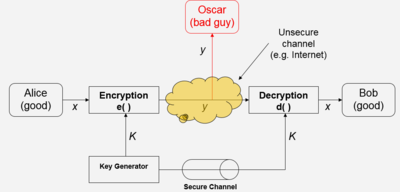
* In Fig 2, x is the plaintext message which Alice wants to send, y is the ciphertext message which has been encrypted, K is the key to encrypt or decrypt the message. | * In Fig 2, x is the plaintext message which Alice wants to send, y is the ciphertext message which has been encrypted, K is the key to encrypt or decrypt the message. | ||
| − | + | ** Encryption equation : <math>y = e_k(x)</math> , where <math>e_k(x)</math> is the encryption function and, | |
| − | * | + | ** Decryption equation : <math>x = d_k(y)</math> , where <math>d_k(x)</math> is the decryption function |
| − | + | ||
* Encryption and decryption are inverse operations if the same key K is used on both sides : | * Encryption and decryption are inverse operations if the same key K is used on both sides : | ||
| Line 40: | Line 39: | ||
* '''However, the system is only secure if an attacker does not learn the key K!''' | * '''However, the system is only secure if an attacker does not learn the key K!''' | ||
| + | ==== 2. Asymmetric Algorithms : ==== | ||
| − | + | * Also known as public-key cryptography. | |
| + | * Unlike Symmetric cryptography, user possesses a secret key as well as a public key. | ||
| + | * We do not discuss this in detail in our slecture but use the references to learn more. | ||
| + | 3. Cryptographic Protocols : | ||
| − | + | * | |
| − | + | ||
---- | ---- | ||
| − | == | + | ==Conclusion== |
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| + | The main focus of slecture is on basics of cryptography uptil symmetric algorithms inlcuding understanding the maths behind it. | ||
| + | |||
---- | ---- | ||
| − | == | + | ==References== |
| − | + | ||
| − | + | ||
| − | + | ||
* C. Paar. Understanding Cryptography. Lecture Notes. Dept. of Electr. Eng. and Information Sciences, Ruhr University. | * C. Paar. Understanding Cryptography. Lecture Notes. Dept. of Electr. Eng. and Information Sciences, Ruhr University. | ||
* C. Paar and J. Pelzl. Understanding Cryptography. A textbook for Student and Practitioners. Springer 2010. | * C. Paar and J. Pelzl. Understanding Cryptography. A textbook for Student and Practitioners. Springer 2010. | ||
Revision as of 05:57, 16 June 2015
A slecture on Cryptography by student Divya Agarwal and Katie Marsh (or anonymous if desired)
Partly based on the Cryptography Summer 2015 lecture material of Paar.
Contents
Introduction to cryptography
The block diagram below shows an overview of the field of cryptology.
Cryptography is the science of secret writing with the goal to hide the orginal message.
Cryptanalysis is the science and sometimes art of breaking cryptosystems.
Cryptography itself splits into three main branches:
1. Symmetric Algorithms :
- Also known as private-key, single-key or secret-key cryptography
- In Fig 2, x is the plaintext message which Alice wants to send, y is the ciphertext message which has been encrypted, K is the key to encrypt or decrypt the message.
- Encryption equation : $ y = e_k(x) $ , where $ e_k(x) $ is the encryption function and,
- Decryption equation : $ x = d_k(y) $ , where $ d_k(x) $ is the decryption function
- Encryption and decryption are inverse operations if the same key K is used on both sides :
$ d_k(y)= d_k(e_k(x))= x $
- However, the system is only secure if an attacker does not learn the key K!
2. Asymmetric Algorithms :
- Also known as public-key cryptography.
- Unlike Symmetric cryptography, user possesses a secret key as well as a public key.
- We do not discuss this in detail in our slecture but use the references to learn more.
3. Cryptographic Protocols :
Conclusion
The main focus of slecture is on basics of cryptography uptil symmetric algorithms inlcuding understanding the maths behind it.
References
- C. Paar. Understanding Cryptography. Lecture Notes. Dept. of Electr. Eng. and Information Sciences, Ruhr University.
- C. Paar and J. Pelzl. Understanding Cryptography. A textbook for Student and Practitioners. Springer 2010.
Questions and comments
If you have any questions, comments, etc. please post them here.
Back to 2015 Summer Cryptography Paar